About CROND
Background
In recent years, the damage caused by cyber attacks, such as targeted campaigns, is becoming more and more significant, and often results in interruptions of business activities and loss of social trust. This lead to an ever growing need to expand the cybersecurity activities and measures, including with regard to education and training.
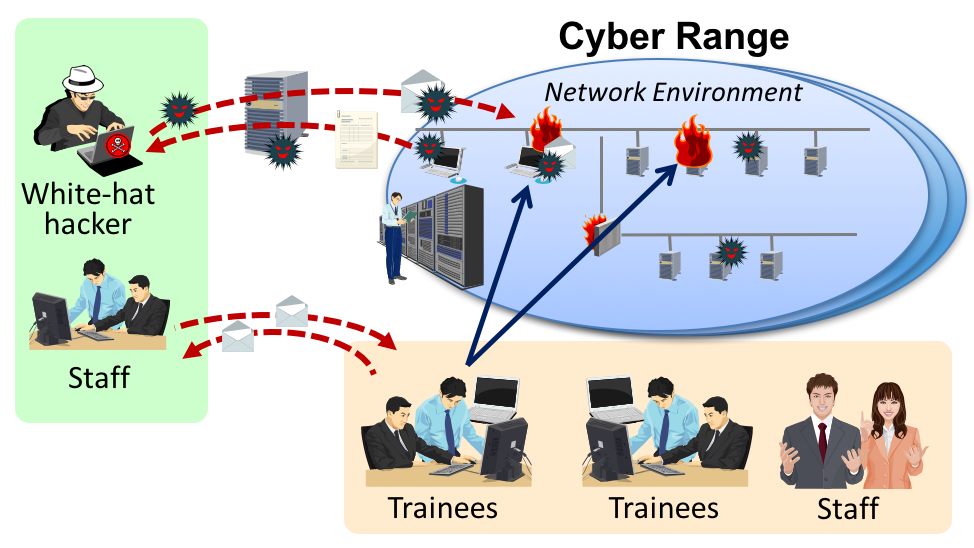
A cyber range is a virtual environment created on a computer and network infrastructure for the purpose of conducting practical cybersecurity training. Cyber range complexity and content need to be adapted to the actual training purpose, such as cyber attack and/or cyber defense, the number of participants and their skill level, and so on. The Cyber Range Organization and Design (CROND) NEC-endowed chair at JAIST studies cyber range architectures and instantiation mechanisms, so that cyber ranges can be deployed in a cost-efficient and time-effective manner.
Overview of the chair
The Dependable Network Innovation Center (founded in 2011; formerly Internet Research Center, founded in 2001), and the Center for Highly Dependable Embedded Systems Technology (founded in 2007) at JAIST have conducted a significant number of large-scale network and security experiments. In addition, these centers have participated in the technical content and curriculum development of the environment used in the training program Cyber Defense Exercise with Recurrence (CYDER) sponsored by the Ministry of Public Management, Home Affairs, Posts and Telecommunications. The Cyber Range Organization and Design chair was created on these foundations to further advance the field of cybersecurity training.
- Chair Name
- Cyber Range Organization and Design (CROND)
- Chair Mission
- Study and develop
mechanisms for the creation of cyber ranges, so as to improve
the effectiveness of cyber-security training for a large number
of participants.
Furthermore, design the related educational programs and teaching materials for the cyber-security training activities that will be conducted using cyber ranges. - Chair Duration
- April 2015 - March 2021
Overview of cybersecurity training