Frequently Asked Question (FAQ)
PickUp
- JAIST-SSO: "AUTHENTICATION FAILED" is displayed.
- JAIST-SSO: I bought a new smartphone. How do I get a one-time password?
- JAIST-SSO: The message "Unknown Error. Please contact Administrator" is displayed.
- Network: I cannot connect to JAIST Wi-Fi
- Network: Guests from other universities want to use the network.
- Remote Access: I cannot access to SSL-VPN system
- Printer: I had trouble with the multifunction printer.
Categories
Account
Account
Please come to RCACI desk (Room I-24) with your student ID.
* If you have already set up a password reset email address, you can reset your password yourself. Please see here for details.
* JAIST-SSO authentication failure can also be due to something other than a password. See the FAQ "'AUTHENTICATION FAILED' is displayed.".
There are various types of employees at JAIST, and the IT services available vary depending on your employee type.
For example, for Microsoft o365, check this page.
https://www.jaist.ac.jp/iscenter/en/software/microsoft/
You can also check the services granted to you in the ‘Available services’ section of the user attributes screen.
https://www.jaist.ac.jp/iscenter/en/useraccount/profile/attribute/
Please see the following pages for each browser.
- Microsoft Edge
Save or forget passwords in Microsoft Edge
View saved passwords - Google Chrome
Manage passwords - Computer - Google Chrome Help
Show, edit, delete, or export saved passwords - Firefox
Password Manager - Remember, delete and edit logins and passwords in Firefox | Firefox Help (mozilla.org)
Managing usernames and passwords - Safari
How to find saved passwords on your Mac - Apple Support
View saved passwords in Safari
JAIST-SSO
JAIST-SSO
The cause of the "AUTHENTICATION FAILED" message varies depending on the usage environment. Please refer to the following page.
When login fails in JAIST-SSO
Please try the following:
(If you have this problem with a device and procedures that have been working fine until now, please try "3. Disable security software".)
- Try authentication in an environment where past authentication information has been deleted
Please try JAIST-SSO authentication using private window mode or a web browser different from the one you normally use (e.g. Chrome or Firefox if you normally use Edge). - Try authentication on another device
If you have a different device than the one causing the problem (e.g., a smartphone if the problem occurs on a PC), please try authentication on that device. - Disable security software and try authentication
We have confirmed cases where "Unknown Error" occurs due to security software. Please disable your security software and try authentication.
Alternatively, please set the "443/tcp (HTTPS)" communication of "auth.jaist.ac.jp" as an exclusion list (e.g. white list, not subject to inspection, etc.) and try authentication. - Try accessing each service from the links on this web page.
- If you are using a non-JAIST SSL-VPN, disconnect and try accessing
"INVALID OTP CODE" is displayed when the One Time Password (OTP) you entered is not correct. The following are possible causes
- You have entered an expired OTP.
One-time passwords are valid for a certain amount of time (a few tens of seconds). Try entering an OTP that has just been issued.
- The time setting of the device is not correct.
OTPs are generated based on time. If the date and time settings of the device generating the OTP are not correct, the OTP generated by that device cannot be used. The time zone must be set to Japan time when you are in Japan.
If you have your digital certificate, you can import it into your browser and present it to log in without being asked to enter the OTP.
[If you have a postcard with your Secret key]
Please register another device as an OTP-generating device (Click here to see how to register). OTP will generate the same value on any device/app when the secret key and time are the same. Compare the values of the two devices, and if different OTPs are generated, it is possible that the time setting or the private key is wrong.
In WinAuth (Windows OTP generation application), you can check the Secret Key by following the steps below.
- Start WinAuth, place the cursor on the OTP code and right click.
- Click "Show Secret Key...".
- When prompted for a password, enter your WinAuth password
- Compare the displayed Secret Key with the Secret Key written on the postcard.
If the strings are different, the OTP has not been registered correctly and you need to register again.
Please try to access from the URL written on this website.
The URLs of various services (WebMail, online storage, SSL-VPN, etc.) are subject to change due to system updates. For the various services that require authentication by JAIST-SSO, the JAIST-SSO screen will be displayed after accessing each page, but you should not bookmark this page. If you want to bookmark this services, please register the URL used in the this website (you can check it by right-clicking the link and clicking [Copy Link]).
You are not authorized to use the service you are accessing.
Please see the page of each service and check if you are included in the target group.
You can check the usage rights for each service on the "Available Service" of Self-Maintenance page.
If you are the target person but do not have the right to use the service, please contact us.
When you renew your PC/smartphone used as an OTP device, please transfer the OTP to a new PC/smartphone.
- If you have the "Secret Key for TOTP (Time-based One-time Password)" postcard
If you have a "Secret Key for TOTP (Time-based one-time Password)" postcard and have not deleted the setting, please refer to the following page to set up OTP.
How to set up One-Time Password (OTP) using postcard
- If you have an old device
If you have an old PC/smart phone that has been used as an OTP generation device, please refer to the following page.
Exporting One Time Passwords (OTP)
- If you don't have the postcard or the old device
Please delete and re-register your current OTP on the campus network.
Deregister authentication factor
One Time Password authentication device registration procedure
Yes, you can.
OTPs are generated using a private key and time.
The same OTP can be generated at the same time on multiple terminals if the same private key is used to set it up.
If you have a "Secret Key for TOTP (Time-based one-time Password)" postcard and have not deleted the setting, please refer to the following page to set up OTP.
How to set up One-Time Password (OTP) using postcard
If you have an OTP-generating terminal, please refer to the following page to export the QR code or secret key string and set it on another device.
Exporting One Time Passwords (OTP)
You cannot receive the "Secret Key for TOTP (Time-based One-time Password)" postcard again.
If the postcard is lost without setting the OTP, or if the device to which the OTP is registered fails after the postcard is discarded, follow the steps below to reconfigure the OTP.
* If you do not have a valid client certificate or FIDO2 settings, you will need to come to JAIST campus to reconfigure.
Network
Network
If you don't know How to connect to JAIST Wi-Fi.
Please read this page "How to connect to JAIST Wi-Fi".
If you cannot connect to Wi-Fi after configuring the settings.
Make sure that the certificate has been imported.
Please accsess UPKI_Manual (Windows / macOS) to see the "Checking the Certificate (PKCS#12 file)" section.
If you can connect before but suddenly cannot connect to JAIST Wi-Fi.
Please make sure that the imported certificate is valid.
- Is it within the validity period?
- Hasn't it revoked?
(How to check the validity/revoked of the client certificate) - Isn't the certificate issued before December 24, 2020?
([Important] Client certificates will be revoked (for issued before 2020/12/24))
If you cannot connect after renewing the certificate.
After renewing the certificate, please refer to the following page to modify your Wi-Fi settings.
How to Replace Digital Certificates for Wi-Fi
Preparation is required for off-campus users to use the JAIST network.
・eduroam
eduroam (education roaming) is the secure, world-wide roaming access service developed for the international research and education community. Members of eduroam participating institutions can use "SSID:eduroam" at JAIST by setting up eduroam usage at their own institutions in advance.
eduroam JP Participants
Map of eduroam participating countries and regions
・eduroam-ID for visitors
Faculty and staff can issue "Visitor's eduroam-ID" to guests, and guests can use the Wi-Fi.
This service is available without application to RCACI and is recommended for urgent guests or a few guests.
* You must issue one eduroam-ID for visitor per one guest.
eduroam-ID for visitors
Also, guests staying at the JAIST International Seminar House will receive a Wi-Fi account that can be used on campus at JAIST only during the period of their stay.
Note that these networks are for off-campus users, and access to campus-only systems is restricted.
In the student dormitory, IP addresses cannot be allocated in a static manner.
As far as concerned, there is no restriction to this kind of usage. However, if everyone starts doing the same thing, the student dormitory connection will collapse as a whole. Since all rooms share a common IP address, please try to use it moderately. In cases where excessive use is noticeable (as judged by the Research Center for Advanced Computing Infrastructure), we will suspend or limit the connection.
Windows XP/vista/7
1. [Start] → [Programs] → [Accessories] → [Command Prompt]
Please enter "getmac /v /fo list". The "Physical address" is the MAC address.
Image here
2.# Those who have LAN network connection#
"Physical address" is the MAC address of the wired LAN which is several lines under the "Local Area Connection" section
# Those who have a wireless network connection #
"Physical address" is the MAC address of the wireless LAN which is several rows under the "Wireless network connection" section
Macintosh(OSX) System Preferences Search
1.Select [System Configuration] → [Network].
2. # Mac OS X 10.5 or later #
Select Ethernet (for wired LAN) or AirMAc(for wireless LAN) and go to "Detail" at the bottom right.
The contents of [Ethernet ID] or [MAC address] displayed when right clicking on Ethernet is the Mac Address.
# Mac OSX 10.3 - 10.4 people #
Change the [Display] menu to built-in Ethernet (for wired LAN) or AirMac(for wireless LAN).
The Mac Address is the content of [Ethernet ID] displayed when clicking on Ethernet which is at the rightmost .
# Mac Ox 10.2 Who #
Change the [Display] menu to built-in Ethernet (for wired LAN) or AirMac(for wireless LAN)
Select the TCP / IP tab. The displayed content of Ethernet address is the MAC address.
Macintosh (OSX) Search by terminal
Go to Macintosh HD> Applications> Utilities> Terminal,
If ifconfig -a is executed, the item of either is the MAC address.
In many cases, en0 is a wired LAN and en1 is a wireless LAN.
Macintosh (OS 9 or earlier)
[Apple Menu] → [Apple System · Profile] → [System Characteristic] → [Network Outline] → [AppleTalk] → Hardware Address This hardware address is the MAC address.
Or you can check it with Control Panel -> AppleTalk -> "File" -> "View Information" control panel -> TCP / IP -> "File" -> "View Information".
Yes, depending on the OS, it is sometimes written as physical address, Ethernet address, Ethernet ID, hardware address, etc.
Yes, if you do not delete it will remain registered as your terminal. If a virus infection is suspected or P2P unauthorized use on that PC within JAIST, you may be held liable.
In order to use JAIST Wi-Fi, you need to import your digital certificate into your PC.
- When you want to continue to use your old PC
①Export the digital certificate that your old PC has.
(Be sure to select "Export secret key.")
②Import the exported digital certificate to the new PC.
③Set up JAIST Wi-Fi on the new PC.
- When you do not use the old PC / When the certificate could not be exported
①Revoke the digital certificate you are currently using.
②Issue a new digital certificate.
③Import the issued digital certificate to the new PC.
④Set up JAIST Wi-Fi on the new PC.
[When you want to use the digital certificate on the old PC]
⑤Delete the revoked digital certificate on the old PC, and import the newly issued digital certificate.
⑥Set up JAIST Wi-Fi on the old PC.
Please refer to the following page for the specific method of each procedure.
If you are not sure how to operate the system by yourself, the help desk will support you. Please bring your old PC and new PC to the reception desk of the RCACI.
From 150.65.108.11 to 150.65.110.97 ; About 599 addresses
Network Registration System
It is a system for applying to connect a terminal to the network. It is to substitute for submitting conventional network connection application form.
No. At Apr 2020, it is applied only to the wired LAN of JAIST house and student dormitories 1-8. It is not applicable for wireless LAN. We are going to expand the scope to whole schools
Yes. The validity period is one year from the registration date
Yes. You can apply for extension at any time. Every time an extension request is made, one year after that date will be set as the expiration date.
It will be handled in the same way as an unregistered devices and will be only be able to access the network connection application system.
Please register your devices again.
Please check the registered device list screen to see if you registered the same MAC address previously. If it is not there, it is thought that someone else registered by mistake. In that case, please let us know the MAC address you tried to register and your account to the Information Society Infrastructure Research Center.
Yes, it will be displayed as the "maximum registered number" on the registered device list screen.
As of now no limit is placed on the number of units. However, extreme things may have an adverse effect on others, such as pressing down on the number of free IP addresses, so please use it moderately. It is intentionally being applied such restrictions at RCACI.
No. In principle, registration is required for all devices that need IP address assignment. Registration is necessary for routers and network compatible printers.
[If you usually use mailer (POP/IMAP)]
Please wait for a while, and then try again.
When you can not access to your account 1 hour after blocking, please contact us.
*For those who have recently changed your password*
For mailers that set the password in advance, please check the settings of your mailer after changing your password. When you change the JAIST account password and do not modify the mailer password, the mailer will continue to use the incorrect password (the password before the change), and email will not be able to be sent or received.
[If you usually use WebMail]
If you see the screen after lockout, please contact us.
If you are not using POP/IMAP, please consider disabling the POP/IMAP.
Reference: POP / IMAP disabled / enabled
If you fail to authenticate (JAIST-SSO) when accessing Webmail, please see the following page.
When login fails in JAIST-SSO
The procedure is roughly as follows:
1. Create an account for new IMAP reception. (Please make it on the e-mail software you use when receiving with POP.)
* Even after changing the settings to stop the automatic mail reception by POP, some mail may still be received by the POP by mail server. So let's enable "Leave copy of mail on server" setting so that mail will stay in the server.
2. Create a new folder in the earlier created account (= make it on the mail server).
3. Copy the mail received by POP to the created folder.
4. When copying of all the mails is completed, delete the POP setting.
Our mail server supports the following protocols
Protocol | Incoming mail server name | Port number | Security |
|---|---|---|---|
IMAP4(Recommended) | imap.jaist.ac.jp | 993 | SSL |
143 | TLS* | ||
POP3 | pop.jaist.ac.jp | 995 | SSL |
110 | TLS* |
Protocol | Incoming Mail server name | Port number | Security |
|---|---|---|---|
SMTP | smtp.jaist.ac.jp | 587 | TLS, SMTP AUTH(LOGIN) |
465 | SSL, SMTP AUTH(LOGIN) |
The mail in the WebMail inbox displays the mail on the mail server.
Therefore please not that if you delete mail on WebMail before receiving it with the PC email software, you will not be able to see it in the PC mail client.
All emails sent to and from our university are checked for viruses.
When a virus is detected in an email, it is delivered to the recipient in the following form.
<Example> For EICAR Test String file
Insert [WARNING: VIRUS REMOVED] in the subject, and deliver it.
From: Sender's email address (※ The email address may be a spoof depending on the virus, so please be careful)
To: Recipient email address
Date: Date
Subject: [WARNING: VIRUS REMOVED] Subject
----
Body of message
----
Attached file (Removed Attachment.txtl)
This attachment contained a virus and was stripped.
Filename: test.txt
Content-Type: text/plain
Virus(es): EICAR-AV-Test
Please look at the basic information on this page and setting up the mail software on this page.
Only people whose User ID is based on student ID number can change their email address.
If you wish to do so please access this page
If you got a new user account by go on to the doctor course, you can move email address from the old one to the new one.
For more information, please see the "Email Address Registration" page.
Mailing List
For the main mailing lists of the faculty and staff, please contact the General Service Section, General Affairs Department.
For students' main mailing lists, please contact the Educational Service Section, Educational Affairs Department.
List of Primary Mailing Lists (Internal Use Only)
If you are the Administrator (Owner) of the Mailing List, you can.
Log in the system and choose the list to confirm from "My lists" or "Search for List(s)" in Menu at the upper part of the screen. Click "Error rate: xx%" in Menu at the left side of List Home screen to find the mail addresses of Members (Subscribers) who fail to receive the email if any.
Maximum data size to send to a ML address is 15 MB (the sum of an attached file and mail text message). If you want to send/receive a large file of more than 15MB, please use JAIST Online Storage System.
Please also read "Failing to send a mail to ML".
The mailing list "xxx-request@ml.jaist.ac.jp" is an email address addressed to the owner of the mailing list "xxx@ml.jaist.ac.jp". It is automatically created when you create a mailing list.
Please note that if you send an email to "xxx-request@ml.jaist.ac.jp", it will not reach the member of "xxx@ml.jaist.ac.jp".
Digital Certificate
Digital certificate/PKI
1. Web browser
For Firefox
Select the "Tools" tab → "Options" → "Advanced" → "Certificates" and press the "View Certificates" button and then "Your certificates" column.
For Internet Explorer,
Select "Tools" → "Internet Options" → "Content" tab and press "Certificates" button. It will be shown in the "Personal" column.
For Safari (Mac OS X)
Open "Keychain Access" (in Applications / Utilities) and search for client certificates. Clicking on the "My Certificate" category makes it possible to see to available client certificates.
For Safari (Windows OS)
Please refer to the contents of "InternetExplorer".
2. Mail software
In the case of Thunderbird, Select "Certificate" tab of "Tools" → "Options" → "Details" and press the "Show Certificates" button. You will see it in the column of "Your certificates".
Please import the downloaded digital certificate (with .p12 extension) into to the browser or mail program that you plan.
If you do not have the digital certificate file at hand or you deleted it, please refer to "I want to retrieve the issued digital certificate file again".
You will receive a notification email within one month of the expiration date of the digital certificate. To continue using the digital certificate service, you need to go through the "application for renewal" process.
- Access the digital certificate management system (accessible only from the campus network)
- Enter your username and password to login
- Press the "New application / renewal application" button to acquire a new electronic certificate
PKI (Public Key Infrastructure) is the "infrastructure" of internet security using public key cryptography technology.
By using this PKI security infrastructure, it is possible for users to use applications and communicate more securely.
- When you are asked for password at 【STEP1】 on the National Institute of Informatics page.
If the screen of "【STEP1】認証情報パスワードを入力" is displayed, the certificate issuance process has failed. (In case of correct operation, the screen of "【STEP2】証明書を発行" will be displayed.)
Please send your user name and a screenshot of the screen to us.
*Clicking the "[発行/issue]" or "[証明書をダウンロード/Download certificate]" button multiple times may cause this to happen.Please click the buttons only once.
- When you are asked for a password (access PIN) during import.
During import, you will be asked for the password for the certificate/private key/encryption/extraction.
-When the certificate file was obtained by downloading it from UPKI
The access PIN (initial password for import) can be confirmed in the J-UPKI system, and please enter it.
-When the certificate file is exported and obtained
Please enter the password you have chosen for the export.
The certificate used for "Authentication Decision" in Firefox cannot be deleted.
To deleted the certificate, please follow the steps below.
- Open the Firefox Certificate Manager.
Click [≡] (three horizontal lines in the upper right corner)
→ Click [Settings]
→ Click [Privacy & Security] scroll down
→ Click [View Certificates] - Deleting authentication settings
Click the [Determine authentication] tab
→ Click the "auth.jaist.ac.jp" line
→ Click [Delete] - Deleting the certificate
Click the [Your Certificates] tab
→ Click the certificate you want to delete
→ Click [Delete]
When "[STEP 1] Enter the Password" screen is displayed, the issuance of the certificate has failed.
Please contact us with your user name and screen view ("[STEP 1] Enter the Password" screen appears).
Inquiry Form
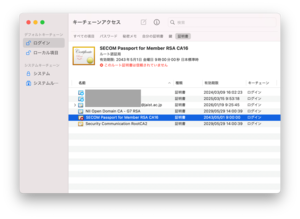
When importing a client certificate, "SECOM Passport for Member RSA CA16" will be imported at the same time as the root certificate. If this root certificate causes an error with the message "This root certificate is not trusted," please check the fingerprint and change the trust settings.
- Check the fingerprints
Please refer to the following page to confirm that the "Fingerprint SHA-1" of "SECOM Passport for Member RSA CA16" is "D5 62 97 10 C1 7B D6 63 91 E8 FC 27 91 9C E1 41 DA B4 7A F8".
https://support.apple.com/guide/keychain-access/view-the-information-stored-in-a-keychain-kyca1085/11.0/mac/14.0 - Change trust settings
Please refer to the following page and change the trust setting of "SECOM Passport for Member RSA CA16" to [Always Trust].
https://support.apple.com/guide/keychain-access/change-the-trust-settings-of-a-certificate-kyca11871/11.0/mac/14.0
The On-Demand Digital Certificate Issuance Support System (J-UPKI) processes digital certificate revocation and issuance requests to the Certification Authority (Secom Trust Systems) via the National Institute of Informatics (NII) system. While requests may be processed within 10 minutes, they may take more than one business day.
If the J-UPKI system or UPKI service is undergoing maintenance, issuance/revocation processing may be unavailable. Please wait until the maintenance is complete.
J-UPKI System Maintenance Information
→Please refer to "Faults/Maintenance" at the bottom right of the top page.
UPKI Service Maintenance Information
→Please refer to this page.
In addition, if you click "Issue" multiple times on the UPKI web screen or go back in your browser, issuance may fail, processing may not complete, or you may be prompted for an unintended password. If the digital certificate issuance/revocation processing is not completed after waiting one business day, please contact the center (contact form here).
online storage
online storage
Students, teachers and researchers can upload up to 100 GB to their personal folders (top area), while staff cannot upload to their personal folders.
For more information, please see 'About folders - personal folders'.
You are not authorised to use the J-Storage Box. There are two possible reasons:
- Not eligible for use
Please check who is eligible to use the J-Stoarge Box. If you are an eligible user but the 403 screen is displayed, please contact us with your user name and status. - Have a free account with a JAIST email address
If you have a free account with a JAIST email address, you are not authorised to use the J-Stoarge Box because we cannot create a JAIST administration account on the J-Stoarge Box. Please contact us after changing the default email address of your free account.
You are eligible to use the J-Storage Box, but your JAIST managed account does not exist. When you have changed your email address, please wait 1~2 working days. If you still cannot sign in after waiting a few days, please contact us with your username.
Shared links for 'People with the link' can only be set for personal files or files under the 'XXX-4.linkable' folder. For more information, see 'About folders'.
If the expiry date is not changed, public shared links ('People with the link' shared links) expire after 1 day (24 hours) and other shared links after 7 days. Shared links set by date expire at around 15:00 Pacific Standard Time (14:00 Daylight Saving Time), 8:00 or 7:00 Japan Standard Time.
Faculty members should create a folder under the "internal folder" and invite members of the laboratory to it.
If you need to invite JAIST unmanaged users (e.g. non-regular students or external collaborators), please create a folder for your laboratory in the "invitable folder".
It is possible to investigate user activity on the file with sufficient information from the responsible person for the file. The file can be restored if it remains in the Trash, but not completely deleted.
If you wish to investigate and restore the file, please contact us with the following information.
- The name of the missing file/folder
- The path where the file was located
- The date and time when the file was last seen.
- (In the case of a shared folder) Can other members see the file?
Yes, you can use Box Drive, Box Edit, Box for Androiod Phones, Box for Android Tablet, Box for iPhone and Box for iPad.
However, RCACI does not provide support for these apps. Please use the web service basically and use the apps at your own risk.
Please refer to the usage instructions. If you have any questions, please contact the IT help desk.
Please sign out once, close all browsers, and then try opening Box again to operate.
If the terms of service are changed, you will be asked to agree again during your next sign-in. We apologize for the inconvenience and ask that you please check and agree.
First, please try using the 'private folder'. (Since it is a folder not intended for sharing, the risk of data leakage is low.) If you want to share files, please upload a test file and check its functionality.
No, folder sharing by 'invitation' is not possible on linkable. Please use linkable folders only when you need to create a public sharing link.
The following points are different:- Capacity: The personal folder is 100GB, while the private folder has no limit.- Eligible Users: The personal folder is for students, researchers, faculty, etc. The private folder is created for staff/faculty and administrative roles.- Sharing Scope: The personal folder allows invitations to internal users and the creation of public sharing links. The private folder has restrictions on invitations and the creation of public sharing links.- Treatment after Completion/Retirement: Access to the personal folder will be lost. For the private folder, faculty data is retained for a certain period, and the data of the administrative role can still be accessed by group members even after one person leaves the organization.
Please contact the center with the names of the deleted (changed) folder and user (group).
Please consult with your supervising faculty member. The faculty member should create a folder for the laboratory under the internal folder (or the invitable folder) and invite the members of the laboratory (students/researchers, etc.) to that folder, in order to prepare a folder that the laboratory members can use for saving research data.
Please invite the user you want to assign member management as a 'co-owner' to the folder. A 'co-owner' has the ability to add and remove collaborators in addition to the rights of an 'editor'.
If the items to share are limited, please use the invitable folder. (If the other user does not have a Box account, they will be prompted to create a free account.)
Since the tasks of research assistants vary, specific folders are not displayed by default (only personal folders that cannot be shared externally). Please request to be invited to the shared folders of the relevant faculty members and departments/centers according to the purpose of the files. For example, if you need to exchange data with a faculty member, please get invited to that faculty member's internal folder. If you are invited as a 'co-owner,' it is also possible to invite other users to the internal or invitable folders. (For example, being invited as a co-owner to the invitable folder allows you to invite external users there for file exchanges.)
Create a work folder under the internal folder of any department related to the work, and invite staff from other departments to it. By inviting them as 'co-owners', the invited staff from other departments can also invite other staff members. It is also possible to invite departments as a group. As long as it is under the created work folder, permissions will be granted hierarchically, so sharing can be done without inviting for each file.
Please use the 'File Request feature'. By accessing the URL issued with this feature, you can upload specific files directly without logging into Box. If you will be exchanging files continuously or need to delete or update uploaded files, please create an account and engage in 'collaboration'.
Please send the invitation to either a 'personal email address' or the 'relevant group.' A Box account for the mailing list '〇〇@ml.jaist.ac.jp' has not been prepared, and it is also not possible to create a new free Box account, so invitations and shares cannot be made. The secretariat has prepared Box groups for each section. You can check the name of the group you [belong to by selecting the shared folder of the relevant section.
[How to confirm the group name of the section you belong to]
1. Hover over the private folder of the department (○○ section〇〇 team-1.private), click on "..." (Other options) → "More actions" → "Manage collaboration".
2. A list of collaborators shared in the team's private folder will be displayed.Names of 3 to 11 characters shared as editors, other than the managing users (whose icons are "jstorage-private" and "jstorage-admin"), will be the group names for that team. By clicking on the group name, you can check the members.
We apologize, but due to licensing reasons, you will not be able to use the J-Storage Box after your resignation/completion. Additionally, you cannot use the JAIST email address for a free account. Furthermore, even if you send an "invitation" using a JAIST email address after your resignation/completion, you will not be able to create a Box account with that email address, and therefore you will not be able to share files.
Your personal folder will become inaccessible once you are no longer eligible to use it. Please download any necessary files. The shared folder for research will be retained for a certain period for the protection of research data. For data that will continue to be used, please move it to your own storage by downloading it, etc. When transferring to another faculty member, please 'move' or 'copy' the files/folders from the shared folder of the retiring faculty member to the shared folder of the currently enrolled faculty member. As for the shared folder of the administration office, group members will still have access, so no transfer operation is necessary.
The Box office administration group will be updated automatically. Please wait.
It is not available. Please wait 1 to 2 business days until it becomes usable.
Please close the Box Drive app, restart your PC, and check if the issue occurs. If it does not get resolved, please use the web service.
Close the screen with the × in the upper right corner and then restart Box Drive from the Start menu. If it doesn't work, please restart your computer and try launching Box Drive again. If the problem persists, please use the web service.
Please restart Box Drive from the Start menu. If it doesn't work, try restarting your computer and then launch Box Drive again. If it still doesn't resolve the issue, please use the web service.
This is the email sent when creating an account for J-Stoarge Box to invite you to a shared folder. It is an intentionally sent email, so please rest assured that it is not spam. Please note that even if you receive this email, you will not be able to use Box until the start date.
It varies depending on the type of folder. Personal folders for faculty/students/researchers are intended for temporary storage of low-priority files and are limited to 100GB. Shared folders are unlimited. However, please note the following points:- If there are many files, there may be delays in searching for files on Box. For shared folders with a large number of stored files, we may ask you to move some to a different folder.- The information environment at JAIST is updated regularly. If a service other than Box is chosen as the next online storage service, you may be asked to migrate your data yourself. Additionally, the capacity of the next service may not be unlimited.
GakuNin RDM
GakuNin RDM
Please see this page.
Remote Access
Remote Access
Please see the FAQ of JAIST-SSO "AUTHENTICATION FAILED" is displayed".
On devices with IPv6 address, the SSL-VPN system menu may not be displayed after user authentication has been successfully.
In this case, please try other methods.
For details, please see this page.
Please try the following.
1.Reinstall the client application
Uninstall the client application (Windows: BIG-IP Edge Client Components, macOS: F5 VPN) and install the application referring to the SSL-VPN connection instructions page.
After that, please access the SSL-VPN and try to connect.
2.Use of alternative methods
Please see this page.
If you have another PC, please check if SSL-VPN connection is available on another PC.
In particular, if your PC is used for SSL-VPN other than JAIST, it may fail to establish SSL-VPN connection.
If the problem cannot be resolved, please refer to the following page and contact us with detailed information.
Requests for Inquiries - SSL-VPN Problems
When using a smartphone with Rakuten Mobile line tethered to a Windows PC and connecting to a VPN on that PC, you may not be able to view the JAIST web page ( https://www.jaist.ac.jp/ ). We have provided logs to the vendor for investigation, but have not been able to identify the cause. The problem is likely to be caused by Rakuten Mobile's line, since it can be used normally when other lines are used.
Rakuten Mobile line users can access the campus network in the following way:
- Use alternative 2 (vpn2)
The SSL-VPN service provides an alternative for when you cannot connect to the official service. We have confirmed that the above problem does not occur with the . alternative 2 (vpn2). Please refer to this page and use vpn2.
* We are sorry that the vpn2 instructions are only in Japanese. If you need help, please come to the reception desk during the hours the help desk is open.
* Alternative services may be suspended without notice. Also, individual inquiries and support may not be available. - Using SSL-VPN with Smartphones
We have confirmed that no problems occur when browsing directly on a smartphone without tethering, even with the Rakuten Mobile connection.
Please refer to this page to set up VPN on your smartphone or tablet device.
The registration for fep has an expiration date. If the expiration date has passed, you will be unable to log in, so please register again. Here is the link for registration.
Have you disabled "Notifications"? If so, go to [Settings] ⇒ [Apps] ⇒ [F5 Access] ⇒ [Allow Notifications] and enable it, then try connecting again.
Virtual Desktop, Thin Client
VDI/ThinClient
Users cannot install software on the JAIST Cloud Desktop that requires installation with administrator privileges.
If you wish to install software for research purposes, etc., please contact the Information Center using the inquiry form, providing the name of the software and the URL of its official website, etc.
However, since the installed software will be available to all users, it may not be possible to install software that requires a license other than a site license, or other drivers or libraries that are incompatible with the system.
The virtual desktop logon password is synchronized with the password used for mail or when using the UNIX system.
To change the password please click on this link
Software
Software
Unfortunately, it is not permitted to continue using the software after leaving our university due to the terms of the license.
Please uninstall this software right away, then purchase new anti-virus software and install it.
No, it is optional.
However, using anti-virus software is required to connect to the campus LAN , so please make sure some antivirus software is installed and running. Also, please use highly reliable products that are certified by the following third party organizations.
- AV-TEST certification
- AV-Comparatives Standard / Advanced / Advanced + Certification
Software that was provided by our center in the past and is not listed page of software cannot be used because there is no valid license at this time. Please delete them if they are still in the device.
Many of the pages can only be accessed from JAIST Network only. For outside user, please use SSL-VPN.
Microsoft Campus Agreement
Microsoft Campus Agreement
We are sorry but it is possible that you are not eligible for licensing. Please inquire with us if this message is displayed and you already have an account or you think you are eligible.
We are sorry but it is possible that you are not eligible for licensing. Please inquire with us if this message is displayed and you already have an account or you think you are eligible.
Also, please contact us if you are a non-regular student.
Visual Studio isn't included in the license program. However, Visual Studio Community can be downloaded for free from https://www.visualstudio.com/downloads/
If the error message during Microsoft365 sign-in includes "SAML assertion is not present in the token.", another Microsoft account may have been affected.
another Microsoft account:
- Personal Microsoft account
- Microsoft account from other universities before entering JAIST
- (Doctoral Students) Account used during master's program
- (Tokyo Satellite students) Microsoft account used by the company
Please try to sign in using a private window.
――――――――――
1.Open Private Window
Open an InPrivite Window / Secret Window / Private Window in your browser.
Tips: Using a Private Window
2.Copy the following URL and paste it into the URL field of the private window to access it.
https://www.office.com/
3.Click "Sign In."
On the Microsoft sign-in screen, enter "username@jaist.ac.jp" and click "Next" and sign in at the JAIST-SSO screen.
――――――――――
You may also be able to sign in with normal browsers by trying the following steps.
- Restart browser
(Please close all browser windows and reopen them.) - Reboot your device
- Delete Cookies
* For the URL to delete cookies, search for keywords such as "microsoft".
If you still see the same error after trying to use a private window or reboot, please contact us with your user name and a screenshot of the error screen.
* This error is displayed on the Microsoft screen; if you encounter an error with JAIST-SSO authentication, please see "When JAIST-SSO login fails".
• Copy the form to your personal Microsoft account
• Download the data in Excel
• Copy the form during the handover
• Create a form with the group as the owner
Once a form file has been moved to a group, it cannot be moved back to your personal folder.
We recommend that you make a copy of the file before moving it to a group, and keep one copy in your personal folder.
Setting up a Website
Web page/Homepage
Content that violates laws and regulations or public policy, infringes copyrights or other rights, or any other content that RCACI deems inappropriate may be removed or moved from the Site without prior notice.
In case you don't want to install a counter program by yourself, please use the counter in the following way.
In the HTML file of the page where you want to put a counter, please add the following description:
<IMG SRC="/cgi-local/Count.cgi?dd=B&df=user.dat&ft=1"ALIGN="BOTTOM">
The user.dat part becomes the file name to save the count number. Please use half-width alphanumeric characters for the user part and set a file name that does not duplicate other users.
The counter design can be set individually.
Click here for counter design and code. Please refer to CGI related websites, books etc. for details of settings.
In addition to the methods described above, you can also install an access counter CGI individually.
→ As of 2011/7, it is confirmed that it is not possible to install a new counter (it is impossible to generate a file to save the counter number). When setting the counter, "Counter datafile" /usr/local/apache2/etc/Counter/data/XXX.dat "must be created first!" will be displayed and will not operate properly. If you wish to install a counter as a provisional measure, please inform www-admin@jaist.ac.jp that you want to set up a counter and file name to save the counter number.
First of all, create a password file with the htpasswd command .
Htpasswd -c /home/USERNAME/.htpasswd USERNAME
(Please add the c option only when creating a new password file. If you already have a password file, adding the c option will cause the contents of the original password file to be entirely replaced.)
Htpasswd /home/USERNAME/.htpasswd USERNAME
(To add a user to an already existing password file, execute htpasswd without the c option.)
Next, put a file named .htaccess like the one below in the directory of the page you want to restrict access to.
Example of .htaccess
AuthUserFile /home/USERNAME/.htpasswd |
AuthName "Page Title" |
AuthType Basic |
require valid-user |
For more about .htaccess, please check relevant websites/books etc
Please place a file named .htaccess like the one below in the directory of the page you want to restrict access to.
Example of .htaccess when accessing only from within campus
order allow,deny |
allow from 150.65.0.0/16 |
allow from 2001:df0:2ed::/48 |
deny from 150.65.176.0/24 |
deny from 150.65.140.0/23 |
deny from 150.65.142.0/24 |
deny from 150.65.143.0/24 |
deny from 150.65.18.31/32 |
deny from 150.65.18.32/30 |
deny from 150.65.18.36/31 |
deny from 150.65.18.38/32 |
| deny from 150.65.18.41/32 |
| deny from 150.65.18.42/31 |
| deny from 150.65.18.44/30 |
| deny from 150.65.18.48/31 |
For more about .htaccess, please check relevant websites/books etc
For the following URLs,
www.jaist.ac.jp/private/ (In the directory /home/www/HTTP/htdocs/private/) )
The pages in the directories are designed to be accessible only from within the university, so if you want to create a page for campus use only, please put the HTML files here.
If you want to set access restrictions in other places, see the FAQs [I want to restrict website access for each connected machine], [I want to restrict website access for each user].
Please click on this link
- www.jaist.ac.jp
It is a WEB server for sharing JAIST information regardless of whether it's within or without campus
- www2.jaist.ac.jp
It is a server for running specific systems, and it is only accessible from within the university. As a bonus feature, it is also possible to use it for practice for personal pages.
However, it is not a server for placing pages for campus internal use. When creating a page for campus use, please place it on www.jaist.ac.jp.
Have you registered your account for www.jaist.ac.jp?
To log in to www.jaist.ac.jp, you need an account for www.jaist.ac.jp.
If you are unable to register、please start here.
Unix server
UNIX server
The Solaris 10 server (sparc 1, 2) does not allow plaintext authentication.
If using a terminal such as TeraTerm, the default authentication method is plain text, so ssh may fail.
In this case, change to the appropriate challenge-response authentication and try to reconnect.
When logging in to the Unix (Solaris 10) server, if you use the Japanese keyboard but the keyboard layout becomes English, open the console and enter the following command.
/usr/local/bin/jp109key
Printer
Printer
Please read "JAIST Printing Service Handling of Consumables"
* The replacement toner may be hidden in a hard to find place, such as under the paper.
* If you cannot find it, please call the telephone number on the multifunction machine from a user that speaks Japanese.
Please see the JAIST Printing Service > Settings & Usage > Printer Trouble page.
Please come to the User Room (I-23).
Large format printers are available from two terminals in the user room.
For detailed printing instructions, please refer to the manuals on the desks of the devices.
For more information, please see the Large Format Printer page.
Others
Others
If your laboratory prepares own servers, please refer to the following.
- Apply for a static IP address
Please refer to the following page to submit a network connection application.
Application for Network Connection
- Setting of DNS and NTP
- Sending and receiving e-mail
About sending and receiving e-mail,
A: When sending mail with hostname from off-campus -> Receiving is rejected due to no destination.
B: When sending mail from the on-campus server -> Authentication (by username and password) is required.
If you want to do the following on own server, please submit "Application to change firewall settings".
a: Receive mail from off-campus to own server on campus
b: Send mail from own server on campus without authentication
- External publication, external access
Basically, the policy is to block communication from outside the campus to the campus servers.
(Excluding pings and ports for servers that are allowed to open to the off campus.)
If you wish to allow communication from off-campus to the on-campus server, such as your own web server, please submit an "Application to change firewall settings".
The macOS web browser "Safari" has a setting to keep IP addresses private.
If this setting is enabled, the device is connected to the campus network, but the communication is considered to be with the off-campus network.
- Cannot access campus-only services ( internal use only page, GAKUMU system, JAIST-LMS, etc.)
- JAIST-SSO requires authentication factors other than password (OTP, certificate)
When accessing campus-only services, please disable the "Hide IP address" setting.
(macOS: Safari -> Settings -> Privacy -> uncheck "Hide IP Address" )
Instructions on how to use/set up the various services provided by the Center are described on this web page.
However, when you still cannot understand after reading the Web page, please contact the IT Help Desk (it-helpdesk[at]ml.jaist.ac.jp) with the following information.
- What services would you like to use?
- What part is not clear to you? How far did you get on your own?
- Environment (device, OS, browser, etc.)
If you are on campus, please come to the reception desk with your device when the IT Help Desk staff is in the rooms. (You can check the availability of the Help Desk from this page.)
Sorry, we do not accept enquiries outside of the services we provide.
(Example:
- Setting up a new PC
- Setting up a printer bought by the laboratory
- Using research software after it has been installed, etc.)
IT helpdesk staff can help resolve these issues to the extent possible.
However, please understand the following points in advance:
- Before consulting, please try to do as much as you can on your own.
- There is a possibility that the problem cannot be resolved.
- Escalation to technical staff will not be provided.
- Priority will be given to support related to the services provided by the RCACI.
If you would like to use the helpdesk, please check the helpdesk work schedule and come to the reception desk with your device.
In addition, users must recognize that they are responsible for managing the devices they use at our institution and must manage them appropriately according to the information security policy.
For details, please see the following pages.